The Dynamics of Passwords

How often do you think about the passwords you’re using? Not only for your website, but also for everything else you do on the internet on a daily basis? Are you re-using any of the same passwords to make it easier to remember them?
We see it all too often: weak passwords used for FTP, database configuration, cPanel, and CMS logins. Everyone has their own password policy, it’s very personal, and usually based on a set of assumptions about online security. Many users choose policies of efficiency over security. Even the paranoid among us have to confront the truth. Like any defensive measure, best practices in password management can only minimize the level of risk.
Password management is a choice, and a habit. By taking a good look at the risks, users can make informed decisions and put better passwords into practice.
History of the Strong Password
Most password strength meters are too soft. The companies that use them know this, but they don’t want users to leave the registration process due to a restrictive password policy. Modern software can guess many so-called “strong” passwords in minutes, and the most common passwords in milliseconds. As password hacking grew in complexity over time, so did the requirements on passwords.
- In the beginning, there were no restrictions on password length or composition.
- Then, it was decided that a basic eight character password was sufficient. All lowercase? Sure!
- Some time later, a symbol, a number, and a capital letter would increase the strength meter.
- Others argued that longer passwords are stronger than complex ones.
- Then we found out how fast a computer program could use a dictionary… and Wikipedia.
Now, using common words, names, and phrases weakens a password significantly. The number of word lists available is growing all the time, and these lists make it faster and easier to crack passwords that we used to think were strong.
![Common Passwords [Source: http://lorrie.cranor.org]](http://blog.sucuri.net/wp-content/uploads/2014/10/badpassword.png)
Common Passwords [Source: http://lorrie.cranor.org]
How Does a Password Get Hacked?
Computers work incredibly fast, and hackers have access to huge amounts of data to help the computer guess more efficiently. On a typical US keyboard there are 94 possible characters. A brute force attack, in its basic form, attempts to guess every possible combination of these characters, until the hacker gets into the account. This method works quickly if the password is fairly short, but can be exhausting with longer passwords. A dictionary attack is a more efficient way to guess long passwords. This uses the same technique as a brute force attack, but instead of guessing all the character combinations, it tries from a list of common passwords and words from dictionaries and literature. Even at almost fifty characters, including symbols, you can’t use the call of Cthulhu as your password. We’re at a point where even the use of common substitutions, L1K3 TH15, are part of most common word lists.
The Rise of Password Breaches
In addition to all of this, even a strong password isn’t a guarantee. The odds of a password getting leaked, due to a data breach or research initiative, are on the rise. With the sheer number of password breaches that continue to occur, hundreds of millions of potentially active passwords are floating around in cyberspace.
Both bad guys and good guys look at password dumps to research the most common passwords and patterns. This data reveals many common tricks that people use to make passwords memorable and strong at the same time.
Clever methods of making your own passwords become transparent with enough data:
- Pattern-based passwords (qwerty678^&*)
- A capital at the beginning and a number and symbol at the end (Password1!)
- Common substitutions (P@ssw0rd)
- Words associated with the user or website (Username@2014)
Once discovered, someone can design a program to exploit these methods via methods known as Brute Force attacks, and in turn, that program can expand the word lists that are used.
A variety of social tactics can also be used to reveal passwords. By spoofing an email address, attackers can lure users with phishing emails that seem legitimate. Similarly, malware on a computer may attempt to scare users into revealing information. In targeted attacks, hackers will use any personally identifying information they can find (such as your birthday, or your dog’s name) to enhance their attack.
For website protection against these kinds of attacks, we recommend using a web application firewall, like CloudProxy. This stops malicious users from breaking into your site.
Reuse is Never a Good Thing
If you don’t use a strong password generator, then you need to ask yourself this question: When multiple sites that you’ve registered with get hacked, and your handmade passwords can be compared, how hard is it going to be for an attacker to figure out your method? While many people reuse entire passwords, a significant number choose a common base and incorporate the site name, or something else to make it unique. There are two problems with this method:
- This method gives a false sense of security by making you believe it’s a safe password.
- This method makes it easy to guess all of your passwords.
Even reusing part of an old passwords is risky. Changing or adding characters to an old password is dangerous, when we know a computer can modify the original password with billions of iterations per second.
Password reuse does have the virtue of being fast and easy to remember. It’s been suggested that passwords can be reused effectively in groups, but the goal here is to get more users on board with password security in general. For those who reuse passwords habitually, it is easier to gradually move to a system of password levels. By creating a few strong, memorable passwords, each one can be reused among accounts that require similar levels of security. The key is to never share a password across security levels. For example, use the strongest password for email and banking, a difficult one for social media, and the weakest password for streaming music.
All reuse scenarios have one thing in common. When one account is compromised, it takes much less effort to compromise the same user’s other accounts. There may be pieces of personally identifying information in low-level accounts that attackers might use in a targeted situation. Password reuse levels are there for those who don’t trust a password manager to save generated passwords for all accounts.
Password Tools Make Security Easier
Generating a password is a great way to have unique, random passwords for every account. There are plenty of password generators online and most offer options to increase the length and complexity of each unique password.
If the idea of having one password is appealing, get a password manager. There are plenty of reviews online to help decide which one is right for you, and they generally work the same way. Make one killer Master Password, then let the application record, scramble, and store all online passwords. After logging in to the password manager, it automatically fills in your passwords as you go. This makes it faster and easier to use strong passwords, and it can also stop keyloggers from capturing your password if you were to type it.
A lot of people still rely on pen and paper. This is dangerous for a few reasons, including loss and theft. One of the better options is to generate a password card. The card is filled with random character combinations. You choose where to start , which direction to go in, and how long it should be. Only you know where your password starts and ends.
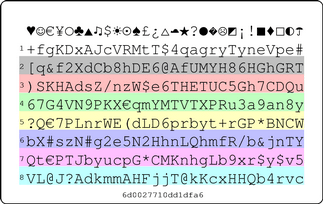
Passwordcard.org
Moving Beyond the Standard Password
With all these restrictions, we might question whether a text-based password is strong enough on its own. Plenty of organizations are embracing two-factor authentication. When you enable 2FA, your phone receives an additional code that you need to enter when logging in from a new device.
We mentioned US keyboards, but it’s good to know that some password fields also accept Unicode characters. These are characters like: €, Γ, and λ. You can find more about them here, and we may write more about them in a future post. If you can use them, great. It’s one way to make your password less guessable.
Finally, biometric authentication allows you to use your unique physical characteristics (such as a fingerprints, heartbeat, or retina) to log into a system. Many business laptops and Apple’s Touch ID offer fingerprint scanning already, for those inclined to use them. We may see passwords replaced, or supported by these alternatives in the future.
Let’s Talk About Entropy
Entropy is the word used to describe how random a password is. The more entropy a password has, the stronger and less predictable it is. Using longer passwords increases entropy exponentially. Adding character sets (numbers, symbols, unicode) increases the permutations available for any length of password. If your password, or part of your password exists in a word list, it isn’t random. If your password is based on a pattern or common base, it isn’t random. When password entropy is low, the password is easier to predict.
We still see that many password fields haven’t evolved past the simple eight-character requirement. It doesn’t help that password strength meters can differ greatly from one to the next. It can be frustrating trying to figure out exactly what makes a password “strong” or theoretically unpredictable. All the while, there is talk of quantum computers that aim to be so fast, they could break any encryption with ease. So, maybe it’s time to download Google Authenticator and get used to 2FA.
In Conclusion
It’s difficult to imagine a future-proof password. Making passwords unique, complex, and longer is a start, all of which are easily accomplished with a decent password manager. Perhaps we’ll see new authentication methods. One thing is certain, as computers evolve in terms of processing speed and storage capacity, requirements on password entropy will need to evolve with it.
What we do know is that password breaches are gaining popularity, and the standard password is not going away. Like anything to do with security, you want to know the risks and put a policy in place that keeps you one step ahead of potential threats. When it comes to your personal accounts and site visitors, protection against brute force and dictionary attacks is an important step to take.