Security Advisory – Critical Vulnerability in the VirtueMart Extension for Joomla!
Advisory for: VirtueMart for Joomla!
Security Risk: High
Exploitation level: Easy/Remote
Vulnerability: Access control bypass / Increase of Privilege
If you’re using the popular VirtueMart Joomla! extension (more than 3,500,000 downloads), you should update right away. During a routine audit for our Website Firewall product we found a critical vulnerability that could be used by a malicious user to easily gain Super-Admin privileges on your website. With super-admin access, the attacker has full control of the site and database.
The bug was discovered and disclosed last week and immediately patched by the VirtueMart team (in record time). They also released the update 2.6.8c to fix this issue.
What are the risks?
Any Joomla! based website running the VirtueMart version <2.6.8c and allowing user registration (default mode for VirtueMart – since it is an online shopping cart for Joomla!), are at risk of a total website takeover. A successful exploit would allow an attacker to become a Super-Administrator and do anything they want, this could include uploading backdoors to your server, running spam campaigns, or distributing malware to your visitors.
If you use an affected version of this extension, please update it as soon as possible! Note that sites using our Website firewall product are already protected against this threat.
Technical details
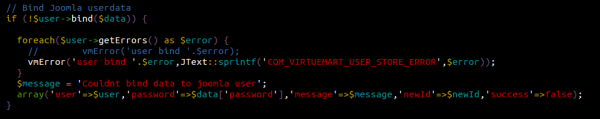
VirtueMart uses Joomla’s JUser class “bind” and “save” methods to handle user accounts information. That’s not a problem in it of itself, but this class is very tricky and easy to make mistakes with.
The bind method roughly does the same thing as PHP’s array_merge function, except for a few points such as live password encryption and the fact that it operates on a class rather than an array.
In the above code snippet, you can see that the extension pass the $data variable (which, at this point in execution, contains the whole $_POST array) directly to the bind() call. While it is an effective way to save/modify user informations, not whitelisting what parameters should be modified is a very bad idea. It basically allows anybody to modify every single variables within JUser’s class scope!
Using this dangerous behaviour, an attacker could modify JUser’s $isRoot, $groups and $_authGroups variables to add their account to the Super-Administrator group, thus giving them full privileges over the target website / environment.
Upgrade VirtueMart as soon as possible!
This is a serious vulnerability and the VirtueMart team did their part by releasing a patch right away. Now do your part and update any site using it.